Quantifying Shadow IT Blast Radius: The Governance Singularity in Distributed Architectures
Shadow IT expands unseen risk. Learn how identity governance and cognitive evaluation shrink the blast radius in distributed engineering teams.
The Perimeter Is a Hallucination
The corporate firewall is a relic. It is a comforting fiction we tell board members to help them sleep. In the modern distributed enterprise, specifically within nearshore engineering contexts, the perimeter has dissolved. It has been replaced by an amorphous, shifting cloud of identity tokens, unmanaged devices, and rogue API keys. This is the domain of Shadow IT. It is not merely a nuisance or a compliance checklist item. It is a structural fracture in the enterprise architecture.
We define the Shadow IT Blast Radius as the maximum potential data exfiltration or systemic corruption capability of a single unmanaged endpoint. In legacy nearshore models, this radius is infinite. A developer in São Paulo downloads a "productivity tool" to parse JSON logs. That tool scrapes the clipboard. The clipboard contains a production AWS secret key. The radius expands instantly from a local laptop to the core of your infrastructure.
This article dissects the mechanics of this threat. We will analyze why legacy governance fails. We will explore how the TeamStation AI platform architecture collapses this radius through rigorous identity management and, critically, through the neuro-psychometric evaluation of the engineers themselves.
The Governance as Code Mandate
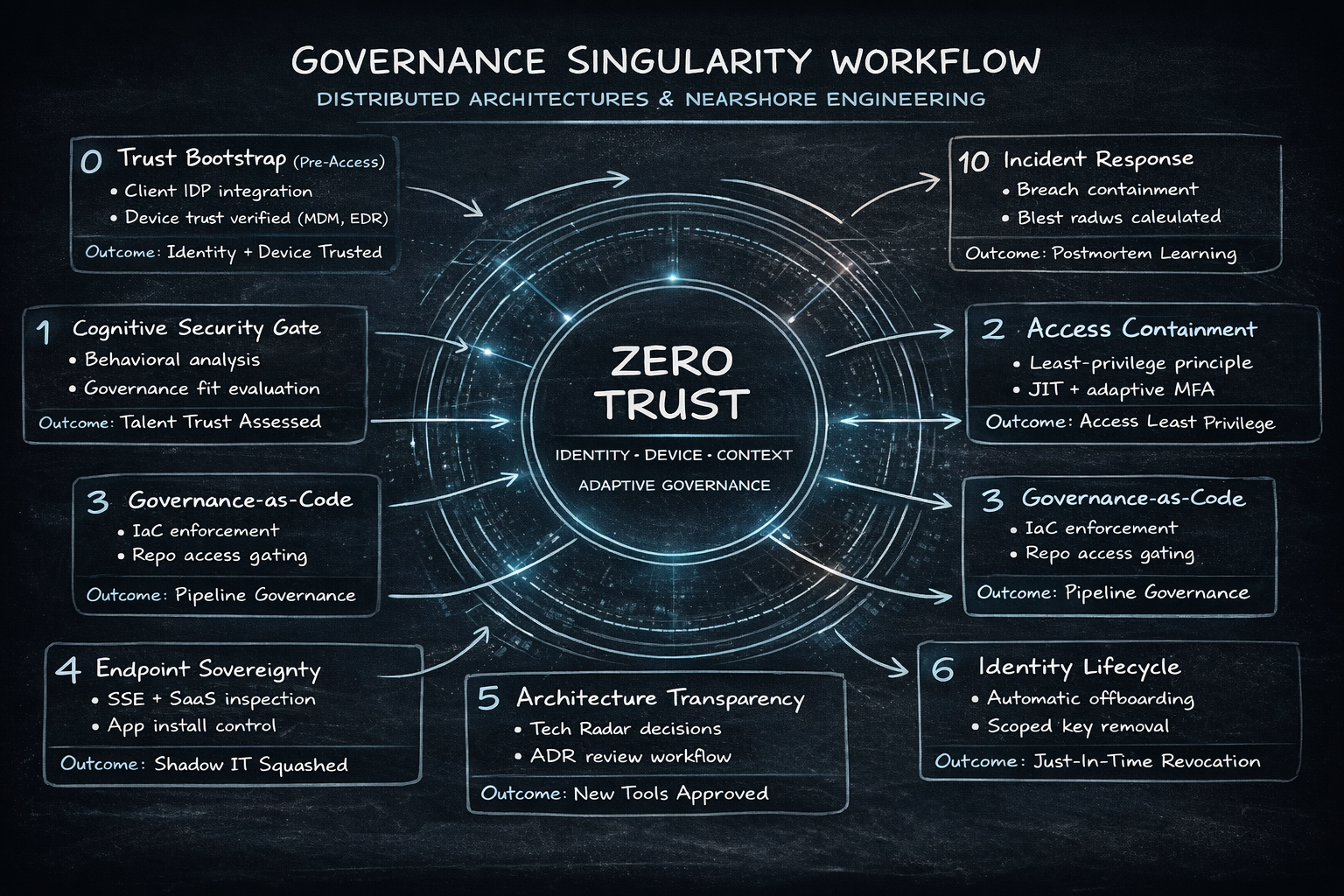
Policy documents are dead. A PDF stored in SharePoint does not stop a junior engineer from spinning up an unapproved EC2 instance. Governance must be code. It must be immutable. It must be enforced at the identity layer. The failure of traditional nearshore vendors lies in their reliance on "trust" and "policy" rather than deterministic architectural controls.
We are witnessing the Compliance Singularity. This is the point where the velocity of software delivery and the rigidity of regulatory requirements (SOC2, HIPAA, GDPR) collide. Without an automated, platformed approach, this collision results in Defect Escape Velocity—where security vulnerabilities bypass manual checks and explode in production.
Section 1: The Anatomy of the Blast Radius
The Shadow IT Blast Radius is not static. It is a function of three vectors: Access Depth, Device Sovereignty, and Cognitive Fidelity.
1.1 Access Depth and the Identity Crisis
In a distributed team, access is often binary. You are in the VPN, or you are out. Once inside, lateral movement becomes the primary threat vector. Shadow IT acts as the bridge. An unapproved browser extension on a developer's machine effectively bridges the gap between the public internet and your internal VPC.
The solution is not a better VPN. The solution is Zero Trust Architecture enforced via Identity Providers (IdP). We do not trust the network. We trust the identity. We trust the device state. If the device is unmanaged, the identity is revoked.
1.2 Device Sovereignty: The VDI Fallacy
Many organizations attempt to mitigate this via Virtual Desktop Infrastructure (VDI). This is a latency nightmare. It destroys developer productivity. It introduces input lag that ruins the "flow state" required for complex algorithmic work.
The alternative is Mobile Device Management (MDM) combined with Secure Service Edge (SSE) technologies. We must manage the endpoint itself. We must enforce disk encryption. We must enforce OS patch levels. We must whitelist applications. This is the only way to contain the blast radius without strangling velocity.
1.3 The Cognitive Vector
This is the overlooked variable. Security is not just software. It is a mindset. A developer with low Architectural Instinct (AI) sees security protocols as obstacles. They will actively seek workarounds. They will use Shadow IT to "get the job done." A developer with high AI understands that security is a quality attribute of the system. They do not bypass controls. They improve them.
This brings us to the critical role of talent evaluation. You cannot govern a team that fundamentally does not respect governance.
Section 2: Axiom Cortex. The Neuro-Psychometric Firewall
Let us be absolutely clear. Axiom Cortex is not a firewall. It is not a piece of security software. It is a Neuro-Psychometric Evaluation Engine. It is the mechanism by which we ensure that the human element of the security equation is robust.
We use Axiom Cortex to quantify the Human Capacity Spectrum. We are looking for specific latent traits that correlate with security hygiene and governance adherence.
2.1 Evaluating Architectural Instinct (AI)
We define Architectural Instinct as the ability to visualize complex systems and anticipate failure modes. A candidate with high AI scores on the Axiom Cortex evaluation understands the implications of introducing a new library. They understand the dependency chain. They understand the Shadow IT Blast Radius.
When we evaluate a candidate for a role, we are not just checking if they know React or Python. We are checking if they possess the cognitive maturity to operate within a governed environment.
2.2 Problem-Solving Agility (PSA) vs. Security Circumvention
There is a fine line between "problem-solving" and "rule-breaking." A candidate with high PSA but low Collaborative Mindset (CM) is a security risk. They will solve the problem of "the firewall is blocking me" by disabling the firewall. This is a catastrophic failure of judgment.
Axiom Cortex uses Phasic Micro-Chunking to analyze how candidates approach constraints. Do they document the blocker? Do they escalate? Or do they hack a solution using unapproved tools? The latter is a Shadow IT vector. We filter these candidates out before they ever touch your codebase.
2.3 The Bias of Trust
Traditional interviewing relies on "gut feel." This is a security vulnerability. A charismatic candidate can talk their way past a security screen. Axiom Cortex eliminates this bias. It evaluates the raw cognitive signal. It measures the Cognitive Fidelity of the candidate's reasoning.
As stated in Nearshore Platformed, "The quest for exceptional technology talent represents a defining challenge of our time... Yet, traditional approaches to talent acquisition often fall short, creating friction, delays, and compromises that hinder progress." We do not compromise on the cognitive security posture of our talent.
Section 3: The Technology Radar and The Immutable ADR Log
Governance must be visible. It must be tracked. We utilize the Technology Radar to define the approved landscape of tools and frameworks.
3.1 The Schema Registry Mandate
Data leakage often occurs at the interface layer. Unmanaged APIs. Ad-hoc JSON structures sent to third-party formatters. We enforce a Schema Registry Mandate. All data structures must be defined. All contracts must be versioned. This prevents the "shadow schema" problem where data flows into unmonitored sinks.
3.2 The Immutable ADR Log
Architecture Decision Records (ADRs) are the audit trail of the engineering mind. When a decision is made to use a new tool, it must be logged. It must be justified. It must be reviewed. This creates a culture of accountability. Shadow IT thrives in the dark. ADRs turn on the lights.
If a team member introduces a new library without an ADR, it is a process violation. It is a signal of Governance Drift. We monitor this drift relentlessly.
3.3 The Open Source License Audit
Shadow IT also exists in the supply chain. The use of libraries with restrictive licenses (GPL) or known vulnerabilities (CVEs) is a form of Shadow IT. It is unmanaged code entering the blast radius.
We integrate Software Composition Analysis (SCA) into the CI/CD pipeline. This is the Security Pillar in action. We block builds that introduce unapproved licenses or vulnerable dependencies. We do not rely on the developer to check. We rely on the platform to enforce.
Section 4: Identity as the New Perimeter
We must discuss the hard mechanics of security. TeamStation AI integrates with enterprise-grade identity providers. We are talking about Okta, Microsoft Entra ID (formerly Azure AD), and Ping Identity.
4.1 SSO and SCIM Provisioning
Single Sign-On (SSO) is the baseline. But SSO is not enough. We need SCIM (System for Cross-domain Identity Management). When a developer leaves the project, their access must be terminated instantly. Across all tools. GitHub. Jira. AWS. Slack.
In legacy nearshore models, offboarding is manual. A ticket is filed. HR emails IT. Days pass. The developer still has access to the repo. This is unacceptable. With SCIM, the termination in the IdP propagates instantly. The blast radius is contained.
4.2 The VDI vs. MDM Debate
We touched on this earlier. VDI is secure but slow. MDM is the modern standard. We deploy Microsoft Intune or Jamf to manage the physical devices of our nearshore talent.
This allows us to enforce:
- BitLocker/FileVault Encryption: If the laptop is stolen, the data is useless.
- Remote Wipe: We can nuke the device from orbit.
- Application Whitelisting: We prevent the installation of Shadow IT tools.
This is Managed Risk. This is how you scale a distributed team without losing sleep.
Section 5: The FinOps Governance Protocol
Shadow IT is not just a security risk. It is a financial hemorrhage. The FinOps Governance Protocol is our method for tracking and controlling cloud spend and SaaS subscriptions.
5.1 The Shadow Bill
Developers spin up resources. They forget to shut them down. They subscribe to SaaS tools on corporate cards. This is "Shadow Spend." It inflates the Total Cost of Engagement.
By routing all infrastructure provisioning through Terraform and all SaaS procurement through a central portal, we eliminate Shadow Spend. We enforce tagging. We enforce budget quotas.
5.2 The SLA/SLO Decoupling
We distinguish between Service Level Agreements (SLAs) and Service Level Objectives (SLOs). Shadow IT often creeps in when teams are under pressure to meet unrealistic SLAs. They cut corners. They use unapproved tools to speed up.
By decoupling these metrics and focusing on Engineering Velocity rather than just uptime, we reduce the pressure that drives Shadow IT. We align incentives.
Section 6: Regional Hubs and Compliance Nuances
The Shadow IT Blast Radius varies by region. Data sovereignty laws in Brazil (LGPD) differ from those in Mexico (LFPDPPP). Your governance strategy must be geo-aware.
6.1 Brazil: The LGPD Fortress
Brazil has strict data protection laws. Hiring in Brazil requires a deep understanding of these regulations. A developer using a personal Gmail account to transfer test data is a violation of federal law.
6.2 Mexico: Proximity and Integration
Mexico offers the advantage of proximity, but the Shadow IT risk remains. We leverage our Partner Network to ensure that devices issued in Mexico meet US security standards.
6.3 Colombia: The Growth Engine
Colombia is a hub for high-growth tech talent. Rapid growth often leads to governance gaps. We counter this with rigorous onboarding and the Axiom Cortex evaluation to ensure that speed does not compromise security.
Section 7: The Role of AI in Governance
We are entering the era of AI-Augmented Governance. We do not just set rules. We use AI to monitor adherence.
7.1 Nebula Search AI and Pattern Recognition
Our Nebula Search AI is not just for finding talent. It is for understanding the patterns of successful teams. We analyze the correlation between specific skill sets and security incidents. We feed this data back into the Axiom Cortex.
If we find that developers with a specific background in "rapid prototyping" tend to bypass security controls, we adjust the weighting in the Latent Trait Inference Engine. We learn. We adapt.
7.2 The Post-Mortem Sanctity
When a breach happens (and it will), the Post-Mortem is sacred. It is not a blame game. It is a learning opportunity. We analyze the root cause. Was it a failure of technology? Or a failure of talent?
Often, it is a failure of Cognitive Alignment. The engineer did not understand the risk. This validates our focus on the Human Capacity Spectrum Analysis. We must hire for capacity, not just skill.
Section 8: Deep Technical Evaluation for Security Roles
To combat Shadow IT, you need security engineers who understand the threat. You need Security Engineering talent that can build the guardrails.
8.1 Evaluating the Guardians
We use specific Axiom Cortex assessments to find these guardians. We do not ask generic questions. We ask about OAuth flows. We ask about JWT signing. We ask about container breakout vectors.
8.2 The DevSecOps Mandate
Security cannot be a separate team. It must be embedded. We hire DevOps Engineers who are also security practitioners. They build the pipeline that blocks the Shadow IT.
Conclusion: The Platformed Future
The era of the "wild west" nearshore is over. The risks are too high. The Shadow IT Blast Radius is too large. You cannot manage this risk with spreadsheets and Zoom calls. You need a platform.
You need TeamStation AI.
We combine the Axiom Cortex for scientific talent evaluation with a robust Security Pillar for operational governance. We eliminate the opacity. We crush the blast radius.
As noted in Nearshore Platformed, "The solution lies not in incremental fixes, but fundamental redesign. It requires embracing a new paradigm that leverages the power of Artificial Intelligence, integrates operations onto a comprehensive platform, and strategically harnesses potential nearshore talent ecosystems."
This is the future. It is governed. It is secure. It is platformed.
Relevant Research & Articles
- TeamStation AI Research
- Research FAQ
- Why Vendor Accountability Disappears
- Why Compliance Slows Teams Down
Technical Assessment Links
Hiring Resources
The perimeter is dead. Long live the platform.
